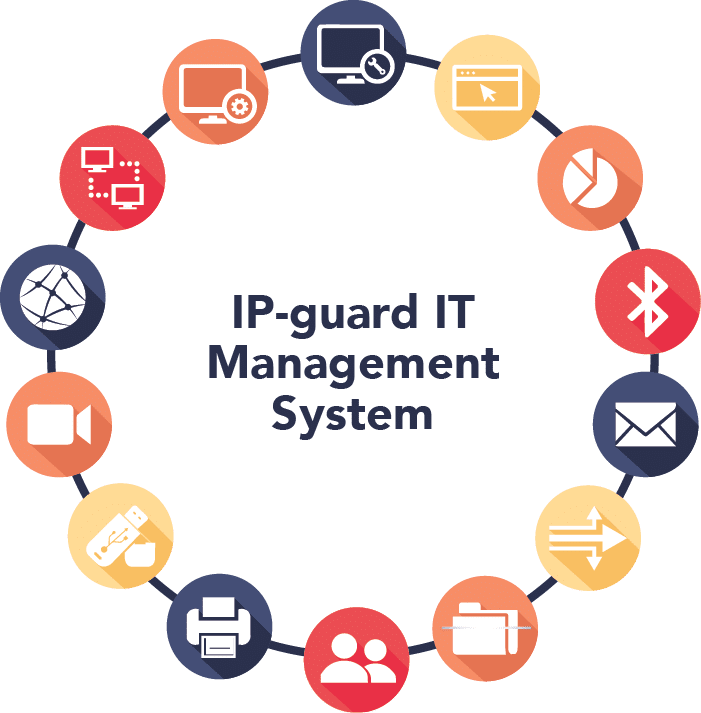
IP-guard Modules
14 Modules for every single need
IP-guard is able to meet diverse management needs. Modules can be optionally selected (minimum: Basic Management Module + any 2 other modules) and repackaged depending on the specific organization’s management requirements.
Become a reseller of any of our products
Be part of the growing business of opportunity and resell products in your region

Application Management
Application Management aims to control and monitor software usage. With appropriate policy settings, improper applications can be blocked easily while the detailed logs help administrators understand user behavior on application usage.
Features
- Easily block applications that are not related to work
- Detailed application usage logs
- Complete analysis reports on application usage
- Real-time alerts on unauthorized application access

Bandwidth Management
Bandwidth Management aims to limit and control bandwidth usage. With the appropriate controls set at specified times, directions, network address, and ports, bandwidth can be allocated to each computer specifically. Detailed traffic statistics help administrators trace abnormal activities while real-time alerts notify them if abnormal traffic is detected.
Features
- Easy to adopt policies that control the bandwidth of each computer in the network.
- Real-time alerts are sent to administrators if any abnormal traffic is detected.
- Detailed traffic statistics and complete analysis reports.
Basic Management
Basic Management is the essential building block of IP-guard. It includes all the basic functions of the computer security software, such as basic information, basic control, basic events logs, basic policy settings, system alerts, and more.
Features
- Multi-language interface support Controls the setting of the control panel, computer management, network configuration, IP/MAC binding and ActiveX controls
- Basic controls include system lock, unlock, turn off, restart and log off of agent computers.
- A powerful search engine to retrieve target information
- Export and import event logs
Device Management
Device Management aims to control removable storage devices, such as communications devices, USB devices, and network devices by executing specific device policies.
Features
- Easily control the access rights of all devices linked to IP-guard
- Execute policies in real-time with no restart action required
- Record detailed audit logs of triggered events

Document Management
Document Management aims to control all document actions in different types of storage media, such as local hard disks, CD-ROMs, Floppies, network drives and removable drives.
Features
- Detailed logs about all file operations include access, modify, delete, copy, create, restore and rename actions
- Powerful control policies on local hard disks, network shared drives, CD-ROMs, and removable storage devices
- Back up specified files based on certain trigger actions such as modification, copy, cut, movement and deletion.
- Powerful search engine to help trace activities faster and with more efficiency

Email Management
Email Management aims to help system administrators control outgoing emails and record emails with attachments, including SMTP/POP3 email, Exchange email, webmail, and Lotus Notes email.
Features
- Control outgoing emails by specifying sender, recipients, email subject and size of the email attachment Record emails with attachments.
- IP-guard supports SMTP/POP3 email, Exchange email, webmail, and Lotus Notes email
- Easy to search a suspect email by email type, address, subject, content, attachment name and size

IM Management
Instant Messaging (IM) Management aims to control outgoing files that are transferred through IM applications to prevent information leakage via this channel. Also, IM conversations’ content can be logged and saved for review in the future.
Features
- Support most popular IM applications, such as MSN Messenger, Yahoo! Messenger, ICQ, Skype, QQ, etc.
- Record chat conversation and instant messages
- Easily block outgoing files
- Back up all outgoing files

IT Asset Management
IT Asset Management aims to manage hardware and software inventory, Windows patch updates and installations, as well as software deployments.
Features
- Complete hardware and software inventory
- Detailed log on hardware and software change
- Add customized assets
- Consistently update Windows patches across computers
- Speed up mass software deployments or upgrades
- Generate reports for further analysis and data mining

Network Management
Network Management aims to control and monitor network communications. With policy controls based on various parameters, including IP addresses, network ports, and traffic directions. System administrators can effectively block selected network ports or download ports to minimize the chances of virus attacks or network drain.
Features
- Easy-to-adopt policies based on parameters of network address, port and traffic directions and more to control network communications.
- Intrusion detection and blocking functions to prevent illegal external access.
- Real-time alerts are sent to administrators upon detection of any prohibited actions.
- Easy to assign network access rights to different groups.

Print Management
Print Management aims to help corporations manage printing facilities and optionally back up the image of printed documents.
Features
- Limit users to use printers
- Detailed print log about local network, shared and virtual printers uses
- Backup printed documents in image files

Remote Maintenance
Remote Maintenance aims to help system administrators or technical support staff shorten their support time. With information, such as real-time reports on computer statuses, and functions, such as remote control and remote file transfer available, support tasks are facilitated whether agent computers are located in the headquarters office, a branch office or a remote site. System administrators can easily control all computers from the IP-guard console.
Features
- Report computers’ status on all running applications, processes, performance, device manager, services, disks, shared status, schedule, user and group status
- Support remote control
- Support remote file transfer
- Enable system administrators to perform remote troubleshooting
Removable Storage Management
Removable Storage Management aims to help companies manage the use of various removable storage devices (e.g. USB flash drives, USB hard disks and MP3 Players) to prevent data leakage and protect systems’ security.
Features
- Disk-based removable storage device authorization
- File-based disk and removable storage encryption
- Only authorized agent computers can access encrypted removable storage devices
- Allow system administrators to register an approved list of removable devices with assigned access controls to only allow these devices to be used

Screen Monitoring
Screen monitoring captures screen activities in real-time and supports multi-screen monitoring. All screen snapshots are saved in proprietary formats. Only authorized users can playback the contents using the built-in viewer of the IP-guard console.
Features
- Real-time monitoring of computer screens’ activities
- Support multi-screen monitoring
- Support screen history review
- Screen history can be exported to video and played through Windows Media Player.

Website Management
Website Management aims to control and monitor users’ web browsing behavior With appropriate policy controls, improper websites can be blocked easily and detailed logs can help administrators understand user behavior on websites.
Features
- Easily block improper websites by setting proper policies
- Detailed web browsing log
- Complete web browsing analytics reports
- Easy-to-read web-browsing statistics on users
- Real-time alerts notify administrators when any unauthorized access occurs
Want to know more?
Download the Full brochure of IP-guard’s Solutions and Modules

